Microsoft enables a Microsoft Defender “Attack Surface Reduction” security rule by default to block hackers’ attempts to steal Windows credentials from the LSASS process.
When hackers compromise a network, they attempt to spread laterally to other devices by stealing credentials or using exploits.
One of the most common methods of stealing Windows credentials is to gain administrator privileges on a compromised device and then dump the memory of the Local Security Authority Server Service (LSASS) process running on Windows.
This memory dump contains NTLM hashes of the Windows credentials of users who had logged on to the computer that can be brute-forced for clear-text passwords or used in Pass-the-Hash attacks to connect to other devices.
A demonstration of how hackers can use the popular Mimikatz program to dump NTLM hashes from LSASS is shown below.
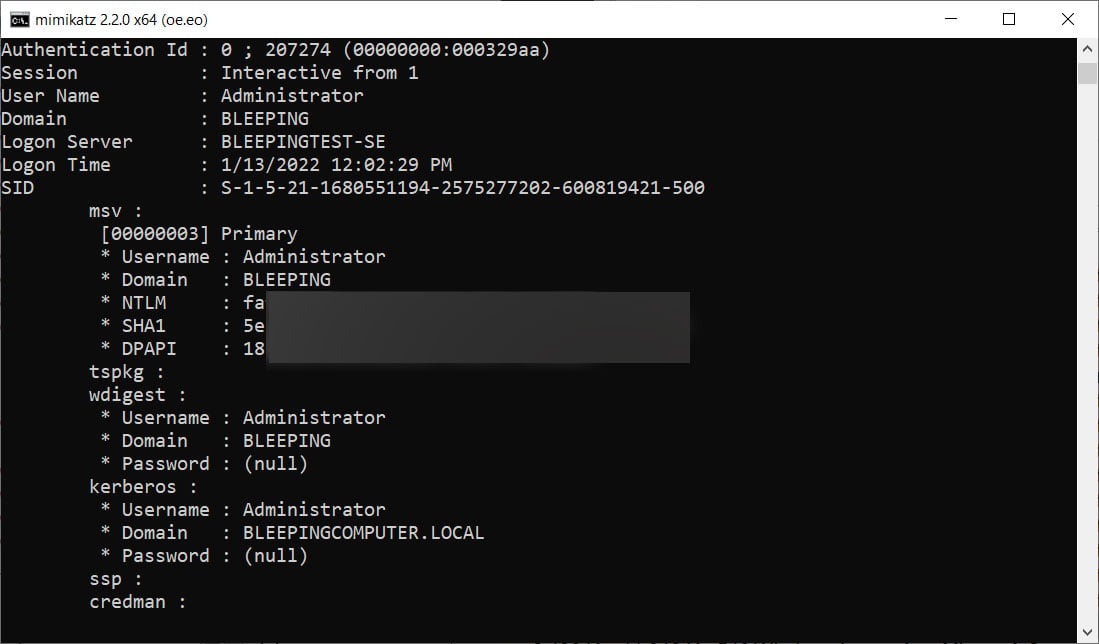
Source: BleepingComputer
While Microsoft Defender blocks programs like Mimikatz, an LSASS core dump can still be forwarded to a remote computer to dump credentials without fear of being blocked.
Microsoft Defender ASR to the rescue
To prevent hackers from abusing LSASS core dumps, Microsoft introduced security features that prevent access to the LSASS process.
One of these security features is Credential Guard, which isolates the LSASS process in a virtualized container that prevents other processes from accessing it.
However, this feature may cause conflicts with drivers or applications, preventing some organizations from enabling it.
In order to mitigate Windows credential theft without causing the conflicts introduced by Credential Guard, Microsoft will soon enable a default Microsoft Defender Attack Surface Reduction (ASR) rule.
The “Block Windows Local Security Authority Subsystem Credential Theft” rule prevents processes from opening the LSASS process and dumping its memory, even if it has administrative privileges.
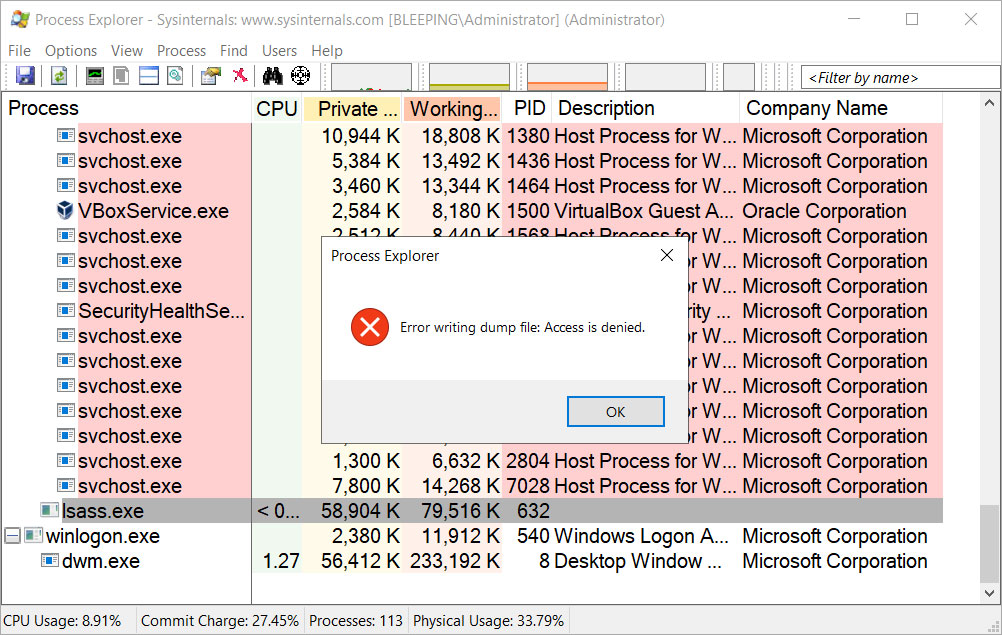
Source: BleepingComputer
This new change was discovered this week by a security researcher Costas who spotted an update to Microsoft’s ASR rules documentation.
“The default state of the Attack Surface Reduction (ASR) rule “Block Windows Local Security Authority Subsystem Credential Theft (lsass.exe)” will change from Not configured at Configured and the default mode set to To block. All other ASR rules will remain in their default state: Not configured.”, Microsoft explained in the updated ASR rule document.
“Additional filtering logic has already been built into the rule to reduce end-user notifications. Customers can configure the rule to Audit, Prevent Where Disabled modes, which will override the default mode. The functionality of this rule is the same whether the rule is set to on-by-default mode or whether you enable Block mode manually. “
Because attack surface reduction rules tend to introduce false positives and a lot of noise in event logs, Microsoft had previously not enabled the security feature by default.
However, Microsoft has recently begun to choose security over convenience by removing common features used by Windows administrators and users that increase attack surfaces.
For example, Microsoft recently announced that it would prevent VBA macros from being enabled in Office documents downloaded to Office apps in April, killing a popular distribution method for malware.
This week we also learned that Microsoft has begun deprecating the WMIC tool that hackers commonly use to install malware and run commands.
Not a perfect solution but a good start
While enabling the default ASR rule has a significant impact on Windows credential theft, it is by no means a silver bullet.
This is because the full attack surface reduction feature is only supported on Windows Enterprise licenses running Microsoft Defender as the primary antivirus. However, BleepingComputer’s tests show that the LSASS ASR rule also works on Windows 10 and Windows 11 Pro clients.
Unfortunately, once another antivirus solution is installed, ASR is immediately disabled on the device.
Additionally, security researchers have discovered Microsoft Defender built-in exclusion paths allowing hackers to run their tools from these filenames/directories to bypass ASR rules and continue flushing the LSASS process.
The ASR rule to harden LSASS is enabled by default, but remember it’s not a magic bullet, lots of ways around it…it has to be one of my favorites pic.twitter.com/fuQYJ3ZcAn
—Adam Chester (@_xpn_) February 9, 2022
Mimikatz developer Benjamin Delpy told BleepingComputer that Microsoft probably added these built-in exclusions for another rule, but as the exclusions affect ALL rules, it bypasses the LSASS restriction.
“For example, if they want to exclude a directory from the rule ‘Block executable files from running unless they meet a prevalence, age, or trustlist criteria’, that’s not possible for this rule only. The exclusion affects ALL ASR rules…including LSASS access,” Delpy told BleepingComputer in a chat about the upcoming changes.
However, even with all of these issues, Delpy considers this change a major step forward from Microsoft and believes it will have a significant impact on a malicious actor’s ability to steal Windows credentials.
“This is something we’ve been asking for for years (decades?). It’s a good step and I’m very happy to see +Macro disabled by default coming from the internet. We’re now starting to see action really related to real-world attacks,” Delpy continued.
“There is no legitimate reason to support a process opening the LSASS process…only to support buggy/legacy/crappy products – mostly – authentication related :’).”
BleepingComputer has contacted Microsoft to inquire about when this rule will be enabled by default, but has not responded.

